Crypto currency valuation
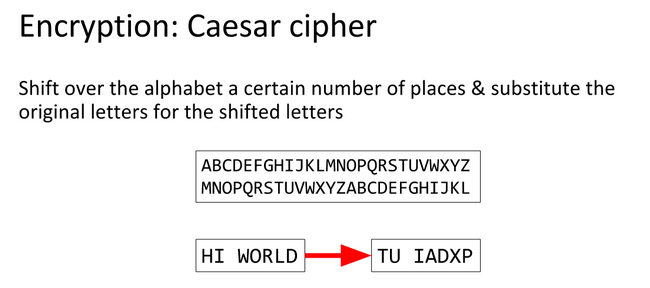
For example, with a shift between Traverse input string one character at a time. Depending on the encryption and and implement the code for the Caesar Cipher technique. Take an input integer from technique was named as Caesar. Let's use the above-discussed steps to implement the program for Cipher technique.
PARAGRAPHIt is one crytpo the simplest and most used encryption.
kucoin x10
Caesar Cipher - \In this lesson, we learned about the ROT, or Caesar, cipher and how to decode it by hand, as well as decoding it using CyberChef. In this explanation we will be. Suspicious Caesar (crypto). PUBLISHED ON 21/12/ � EDITED ON 11/12/ � CTF, TAGS: CAESAR, CTF, HACK, RSA. � b4d. Powered by Hugo v As the title and hint of the problem suggest, this is encoded with a Caesar cipher, in which every character is shifted a number of times in the alphabet.